[qode_elements_holder number_of_columns=”one_column”][qode_elements_holder_item vertical_alignment=”middle” advanced_animations=”no” item_padding=”0 50% 0 0″ item_padding_1024_1280=”0 43% 0 0″ item_padding_768_1024=”14% 4% 17% 0″ item_padding_600_768=”14% 4% 17% 0″ item_padding_480_600=”16% 0 26%” item_padding_480=”16% 0 26%”]
Sally uses intelligence methodology to bring
[/qode_elements_holder_item][/qode_elements_holder]
Sally uses intelligence methodology to bring
light to your digital security’s blind spots.
Have the most exhaustive report to manage all your digital risks: exposed credentials, Infostealers, data leaks…
#datadrivensecurity
[button size=”large” style=”white” target=”_self” hover_type=”default” text=”WHAT CAN WE GIVE YOU?” link=”#contact” color=”#ed6874″ hover_color=”#ffffff” background_color=”#ffffff” hover_background_color=”#ed6874″]
Download the report content.
The report
Enrich today’s Assume Breach Strategy
with Prevent Breach Strategy.
Fight your enemies before they reach you.

Infostealers
& Botnets

Stolen
Credentials

Technical
vulnerabilities

Digital
Exposure
Everything we need is your domain.
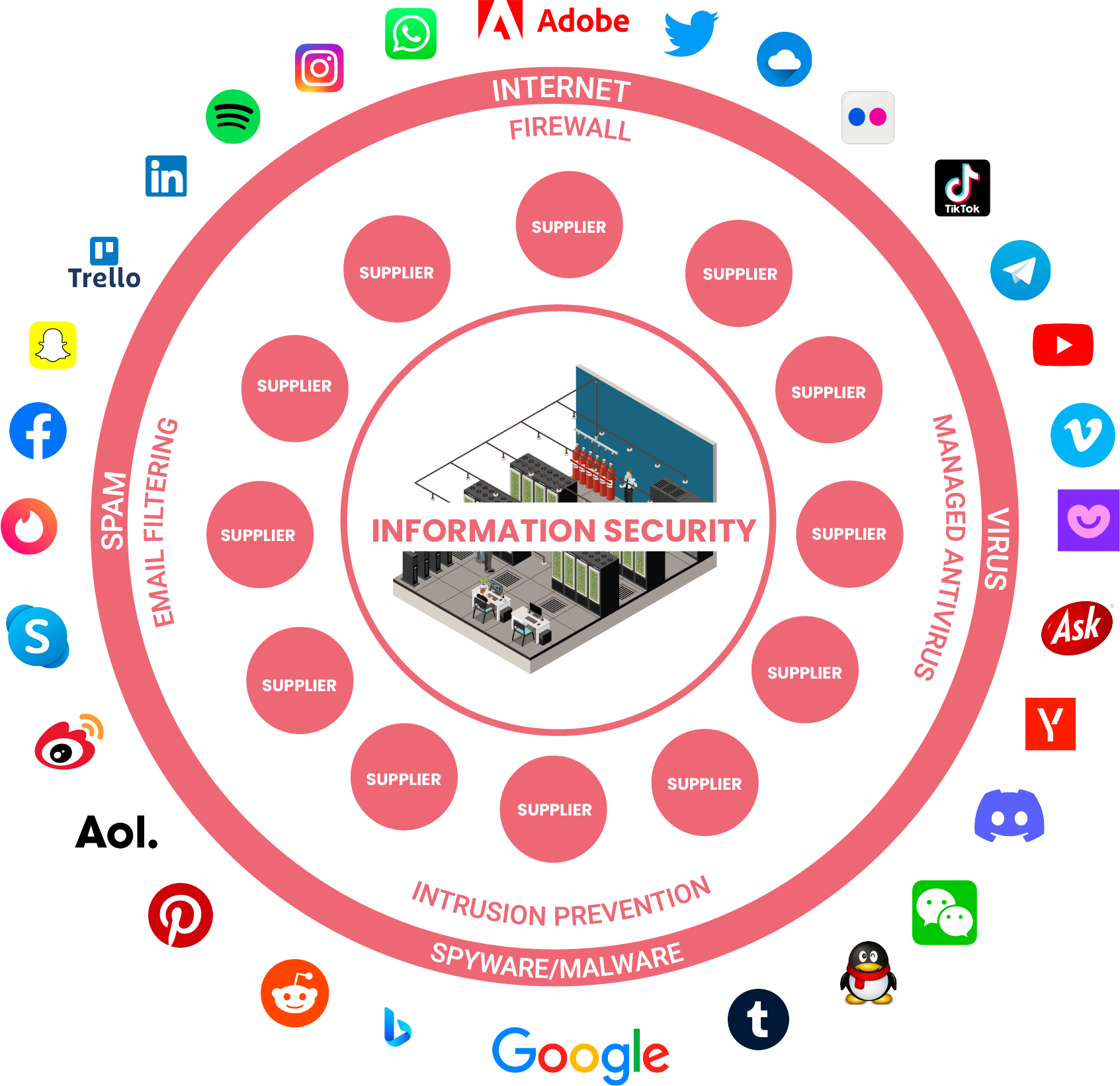
We at Sally have modelled the threat landscape outside the IT-Security Intelligence and used Intelligence and privilege data to create automated digital rounds for surveillance from outside of the IT-Security Perimeter (outside surface), supply chain, digital exposure, and human factor. In other words, we look for human, technical, digital and supplier vulnerabilities to manage digital security and mitigate digital risks.
[icons icon_pack=”font_elegant” fe_icon=”icon_quotations” size=”fa-3x” type=”square” custom_size=”80″ custom_shape_size=”53″ border_radius=”200″ border=”yes” target=”_self” icon_color=”#000000″ icon_hover_color=”#1e1e1e” border_color=”#ffffff” border_width=”2″ background_color=”rgba(255,255,255,0.01)” hover_background_color=”#ffffff”]
A wise man said once: You carry on the war far from the main walls of your fortress. And the enemy meets you there, and with difficulty will he come close to the easily-scaled battlements of your castle. And if he does come, he comes exhausted.
Sally’s intelligence team has access to over 99K breaches containing approximately 106B total PII records circulating across the deep and dark web.
Breakdown of types of Breaches and Exposed Records
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Breaches/Leakages” title_color=”#ffffff” percent=”55″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Records with e-mail” title_color=”#ffffff” percent=”61″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Combo Breaches” title_color=”#ffffff” percent=”41″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Records without e-mail” title_color=”#ffffff” percent=”39″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Breaches with only e-mail” title_color=”#ffffff” percent=”5″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
[progress_bar title_tag=”h5″ percent_font_weight=”500″ gradient=”no” title=”Breaches with e-mail and password” title_color=”#ffffff” percent=”3″ percent_color=”#ffffff” percent_font_size=”20″ active_background_color=”#ed6874″ noactive_background_color=”#f2f2f2″ height=”5″ border_radius=”0″]
Knowing these data are available,
Do you dare not to know?
Look at the info we are able to give you